#djvu #tfude #pdff #rumba #tro #promos #adobe #pdff #tro #tfudeUnlock Files Encrypted with Ransomware DJVU, Adobe, PDFF, TRO, TFUDE & RUMBA LotusGeekNote. Melalui halaman Facebook Virus Info, Cara untuk membuka file yang sudah terkena virus ransomware dengan menggunakan Decryptor STOP. Decryptor untuk STOP Ransomware ini dibuat oleh Emsisoft dan Michael Gillespie yang membantu Anda mengembalikan file yang dienkripsi oleh ransomware mulai dari berbagai varian type ransomware secara GRATIS. Feb 28, 2021 STOP/DJVU Decryptor and MediaRepair are two main utilities which can help to repair OR decrypt files locked by STOP/DJVU ransomware. The decryptor is an encrypted-file decryption tool created by Emsisoft and Michael Gillespie and published on October 18, 2019. It is currently capable of decrypting 148 virus versions out of 160. Emsisoft Decryptor for STOP Djvu will allow for the decryption of files held hostage by the STOP Djvu strain of ransomware. There are limitations on what files can be decrypted. For all versions of STOP Djvu, files can be successfully decrypted if an offline key encrypted them that Emsisoft has.
- Rumba Ransomware Decryptor 1
- Rumba Ransomware Decryptor Version
- Rumba Ransomware Decryptor 2
- Rumba Ransomware Decrypt
- Rumba Ransomware Decryptor 3
SPECIAL OFFER
Important for .rumba Files Virus victims!Files, encrypted by .rumba Files Virus could not be the only harm done to your computer. .rumba Files Virus may still be active on your machine and may spread to other computers on your network. To detect if you are still at risk and eliminate the threat, we recommend downloading SpyHunter.Further information on SpyHunter and uninstall guide. Before proceeding, please see SpyHunter’s EULA and Threat Assessment Criteria. The Privacy Policy of SpyHunter can be found on the following link. Bear in mind that SpyHunter scanner is completely free. If the software detects a virus, you can also remove it with a delayed removal or by purchasing SpyHunter’s full version. Also, keep in mind that SpyHunter cannot restore your files and is simply an advanced malware removal software.
This article is made to explain to you what is the .rumba file ransomware and show you ways via which you can remove it and try restoring your files.
If your computer was recently infected by .rumba files ransomware, then you have come to the right place. The .rumba ransomware virus is from the cryptovirus kind, meaning that it aims to encrypt the files on your computer in order to make them seem corrupt at least until you pay ransom to get them back. The ransomware then adds the .rumba file extension to the files of the computers encrypted by it and also drops the _openme.txt ransom note. If your computer has suffered and infection by the .rumba files virus we suggest that you read this article thoroughly. It aims to show you ways via which you can remove the .rumba file ransomware and try to recover your encoded files.
| Threat Name | .rumba Files Virus |
| Category | Ransomware virus. |
| Main Activity | Infects the computer after which encrypts important documents and holds them hostage until a ransom is paid. |
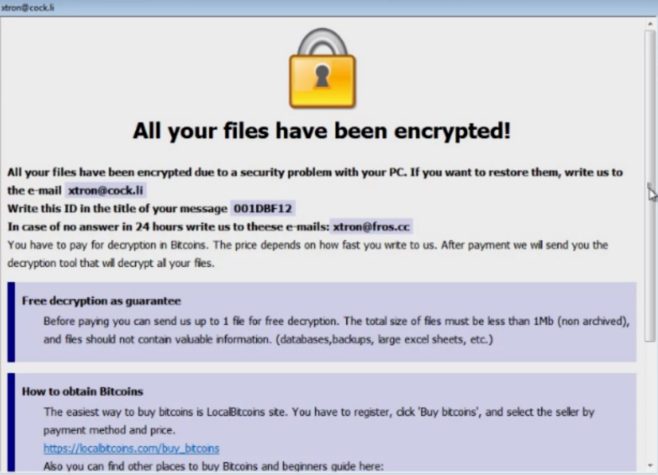
| Signs of Presence | Files are encrypted with a .rumba file extension which has a unique ID and the e-mails of the crooks and ransom note is dropped with ransom instructions.. |
| Spread | Via malicious e-mail spam and set of infection tools. |
| Detection+Removal | |
| File Recovery | Download Data Recovery Software, to see how many files encrypted by .rumba Files Virus ransomware you will be able to recover. |
Which Files May Get Affected by .rumba Files Virus Ransomware?
.rumba Files Virus Ransomware serves as a typical file-encoding Trojan. As soon as it gets access to your machine, this cryptomalware will perform a quick scan to find the paths to all of your personal files. The targeted data includes all MS Office documents, your precious photos and videos, your databases, the program files, etc. Only a few files such as the ones related to the core Windows processes may be spared. Once the operation ends, you will notice a threatening lockdown message on your desktop and the default file extension will become ‘.dll’. The cyber criminals give the victims only several days pay the ransom of Bitcoins, or else they threaten to delete forever the decryption key. The purpose of this frightening message is to shock the person and make him act irrationally. The victims often feel as the only solution to the issue is to pay the money. In reality, all specialists unanimously recommend not to follow the instructions of the hackers for several different reasons.How to Protect Yourself from .rumba Files Virus Ransomware?
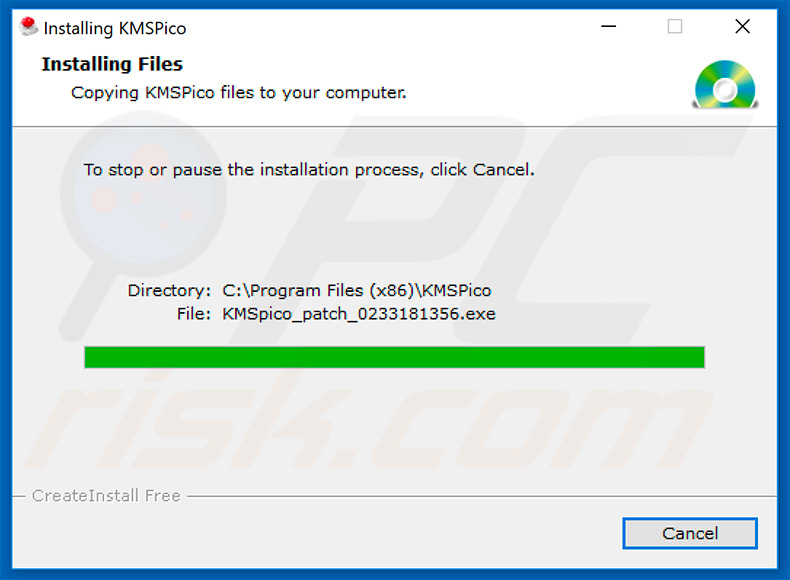
This ransomware may cause huge and often irreversible damage to the affected machines. Fortunately, you can prevent the infection as long as you are vigilant during your online sessions. This Trojan isn’t known to use some unique methods to infiltrate the defences of your computer. The most probable cause for .rumba Files Virus Ransomware to enter is via spam emails. You may receive a message with a shocking content, encouraging you to either click on a malicious link or download a compromised file. The hackers have a whole arsenal of tools to manipulate you into doing so. For example, they may claim to represent an international bank or some popular shipping company. If they address you without mentioning your name, the email is probably a scam and you should ignore it. Unfortunately, if you simply click or download the infected file, your action will most likely be enough to activate the harmful codes of .rumba Files Virus Ransomware. In this case, only a credible security solution may be able to prevent the forthcoming damage.
The _openme.txt ransom note’s contents:
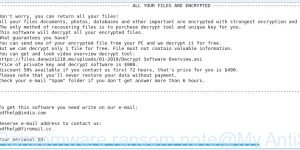
———————————————- ALL YOUR FILES ARE ENCRYPTED ———————————————–
Don’t worry, you can return all your files!
All your files documents, photos, databases and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees do we give to you?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information
Don’t try to use third-party decrypt tools because it will destroy your files.
Discount 50% available if you contact us first 72 hours.
—————————————————————————————————————————
To get this software you need write on our e-mail:
[email protected]
Reserve e-mail address to contact us:
[email protected]
Your personal ID:
[redacted 43 alphanumeric chars]
The main reasons not to pay the ransom are two. First, you may not receive the promised unlocking key even after doing exactly as the hackers demand. They often scam the victims because the Bitcoin platform doesn’t allow refunds and the people have no way to get their money back. The second reason not to finance cyber criminals is that your money will only motivate them to create more aggressive ransomware like .rumba Files Virus. On the other hand, if their attacks are in vain, they may stop spamming the web with such malicious Trojans. These parasites require quite some efforts to be created professionally and spread efficiently.
Once you decide not to pay the ransom, there are several other ways that may help you decrypt your personal files. You should begin the attempts by removing all traces of the malware. If you fail to delete .rumba Files Virus Ransomware properly, it may decrypt your files once again in the future or spread to other connected devices. The manual removal is not the recommended solution since it requires expert-level knowledge in computers. The most reliable tactic is to use dedicated security software that has added F.rumba Files Virus Ransomware to its database. Once the scan finishes, you should try some of the programs for restoration of files or the integrated System Restore feature. If you are lucky enough to have a spare copy of your files on some external device, you can import them back to your computer safely.
Booting in Safe Mode
Rumba Ransomware Decryptor 1
For Windows:
1) Hold Windows Key and R
2) A run Window will appear, in it type “msconfig” and hit Enter
3) After the Window appears go to the Boot tab and select Safe Boot
Cut out .rumba Files Virus in Task Manager
1) Press CTRL+ESC+SHIFT at the same time.
2) Locate the “Processes” tab.
3) Locate the malicious process of .rumba Files Virus, and end it’s task by right-clicking on it and clicking on “End Process”

Eliminate .rumba Files Virus‘s Malicious Registries
For most Windows variants:
1) Hold Windows Button and R.
2) In the “Run” box type “Regedit” and hit “Enter”.
3) Hold CTRL+F keys and type .rumba Files Virus or the file name of the malicious executable of the virus which is usually located in %AppData%, %Temp%, %Local%, %Roaming% or %SystemDrive%.
4) After having located malicious registry objects, some of which are usually in the Run and RunOnce subkeys delete them ermanently and restart your computer. Here is how to find and delete keys for different versions.
For Windows 7: Open the Start Menu and in the search type and type regedit –> Open it. –> Hold CTRL + F buttons –> Type .rumba Files Virus Virus in the search field.
Win 8/10 users: Start Button –> Choose Run –> type regedit –> Hit Enter -> Press CTRL + F buttons. Type .rumba Files Virus in the search field.
Automatic Removal of .rumba Files Virus
Step 1:Click on the button to download SpyHunter’s installer.
It is advisable to run a scan before committing to purchase the full version. You should make sure that the malware is detected by SpyHunter first.
Step 2: Guide yourself by the download instructions provided for each browser.
Step 3: After you have installed SpyHunter, wait for the program to update.
Step4: If the program does not start to scan automatically, click on the “Scan Computer Now” button.
Step5: After SpyHunter has completed with your system`s scan, click on the “Next” button to clear it.
Rumba Ransomware Decryptor Version
Step6: Once your computer is clean, it is advisable to restart it.
Recover files encrypted by the .rumba Files Virus Ransomware.
Rumba Ransomware Decryptor 2
Method 1:Using Shadow Explorer. In case you have enabled File history on your Windows Machine one thing you can do is to use Shadow Explorer to get your files back. Unfortunately some ransomware viruses may delete those shadow volume copies with an administrative command to prevent you from doing just that.
Method 2: If you try to decrypt your files using third-party decryption tools. There are many antivirus providers who have decrypted multiple ransomware viruses the last couple of years and posted decryptors for them. Chances are if your ransomware virus uses the same encryption code used by a decryptable virus, you may get the files back. However, this is also not a guarantee, so you might want to try this method with copies of the original encrypted files, because if a third-party program tampers with their encrypted structure, they may be damaged permanently. Here are the vendors to look for:
Rumba Ransomware Decrypt
- Kaspersky.
- Emsisoft.
- TrendMicro.
Rumba Ransomware Decryptor 3
Method 3: Using Data Recovery tools. This method is suggested by multiple experts in the field. It can be used to scan your hard drive’s sectors and hence scramble the encrypted files anew as if they were deleted. Most ransomware viruses usually delete a file and create an encrypted copy to prevent such programs for restoring the files, but not all are this sophisticated. So you may have a chance of restoring some of your files with this method. Here are several data recovery programs which you can try and restore at least some of your files: